Allion Labs
Bluetooth is a short-range wireless communication standard used between various technological products such as mobile phones, laptops, tablets, earphones, smart speakers, smart wearables, and many more. As Bluetooth becomes mainstream, related security risks are also emerging. In this article, we will discuss the most common security risks and attacks, as well as their respective solutions.

Wireless attacks
Since Bluetooth is a wireless technology, hackers can utilize specific types of wireless hacking to control and steal device data. Common attacks are listed below:
- Bluesnarfing
- Bluejacking
- Bluebugging
- Car Whisperer
- Denial of Service
- Fuzzing Attacks
- Pairing Eavesdropping
- Secure Simple Pairing Attacks
Bluetooth Protocol Security Vulnerabilities
The Bluetooth Protocol itself has vulnerabilities that can be exploited by hackers to gain access to the two connected devices to steal sensitive data or device controls. Common vulnerability attacks include:
Key Negotiation of Bluetooth (KNOB) Attack
The KNOB is a type of attack on Bluetooth technology security vulnerabilities that takes place during encryption in the pairing process. Primarily, the Link Manager Protocol (LMP) is responsible for the management of the link between Bluetooth devices, including the encryption key length. In a KNOB attack, the hacker takes advantage of the flaws in the LMP to forcefully reduce the encryption key length through the request message “LMP_encryption_key_size_req”. The short encryption key is then easily decoded, allowing the hacker to gain full access to and freely tamper with the communication between the two connected Bluetooth devices.
KNOB attacks affect a variety of Bluetooth devices, including Basic Rate/Enhanced Data Rate (BR/EDR) devices. To prevent KNOB attacks, manufacturers and software developers should take preventative measures such as utilizing longer encryption keys that are less susceptible to forced alteration and users should use the latest device software with the latest security patches.
Bluetooth Impersonation Attacks (BIAS)
The BIAS Attack is a type of attack targeting Bluetooth security, where the hacker impersonates a previously paired device to bypass security and gain unauthorized access. BIAS attacks specifically target Bluetooth devices that use Basic Rate/Enhanced Data Rate (BR/EDR).
BR/EDR refers to the two major modes of operation that provide a higher throughput, often used for data-intensive applications such as in multimedia and text files. The Bluetooth SIG has announced security recommendations and fixes for BIAS attacks. The Bluetooth Core Specification Versions 5.1, 5.2, and on contain the fixes for BIAS attacks.
According to the Bluetooth SIG, manufacturers should update firmware and drivers while software developers should implement stricter Bluetooth security policies like the mandatory use of secure pairing mechanisms.
BlueBorne
BlueBorne is a type of attack that targets Bluetooth devices. The hacker can discreetly control an infected Bluetooth device to obtain sensitive user data and messages, install malicious software, and even control the infected device. This attack not only affects individual device users but also business device users, capable of causing massive data leaks and network security risks.
BlueBorne attacks are dangerous because they do not require user interaction, which means it operates stealthily without being noticed.
To prevent BlueBorne attacks, users should keep device software updated to obtain the latest security fixes, while manufacturers and software developers should actively fix the vulnerabilities and strengthen Bluetooth security mechanisms.
SweynTooth
SweynTooth is a type of attack that affects Bluetooth Low Energy (BLE) devices. SweynTooth attacks target BLE’s Bluetooth stack implementation, affecting several protocol layers, including:
- Logical Link Control and Adaptation Protocol (L2CAP): responsible for establishing and transmitting data between Bluetooth devices.
- Attribute Protocol (ATT): a core protocol in BLE, responsible for defining how Bluetooth devices discover and operate services and characteristics.
- Host Controller Interface (HCI): an Bluetooth interface used to transmit commands and data between host and controller.
SweynTooth causes a variety of security issues, including denial-of-service (DoS) vulnerabilities, firmware crashes, and device takeovers. These vulnerabilities affect a myriad of devices from many Bluetooth chip manufacturers, such as consumer electronics, industry equipment, and medical equipment.
To prevent SweynTooth attacks, manufacturers must fix the affected stack implementation and provide firmware updates to mitigate the attack. Users must ensure their devices have updated to the latest software to ensure the latest security fixes. These measures will help protect the security of Bluetooth devices.
BlueFrag
BlueFrag targets L2CAP vulnerabilities in Bluetooth. L2CAP is a protocol layer within Bluetooth, responsible for establishing and transmitting data between Bluetooth devices.
A BlueFrag attacker sends a special L2CAP packet that causes memory corruption. The attacker then executes arbitrary code on the victim’s device, disclosing private data or handing over complete control to the attacker.
These attacks primarily target devices running on Android 8.0 and 9.0, because there are vulnerabilities in the Bluetooth stack implementation. The same issues are not found in iOS systems due to differences between the Bluetooth stack implementation. Google has announced a security update to mitigate the issue, and users should ensure they obtain the latest security fixes. Furthermore, manufacturers and software developers should continue to discover and fix Bluetooth vulnerabilities to ensure the safety of users.
Bluetooth has become an indispensable part of technology nowadays, While enjoying the convenience delivered by Bluetooth, it also brings us security risks and makes us easy targets for hackers. Individuals and businesses must be aware of these Bluetooth security risks and takes the required measure to protect their devices and data, while manufacturers should take the responsibility to ensure device security.
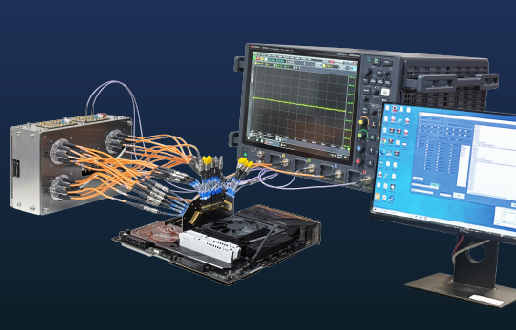
Allion’s Cybersecurity Lab is Looking Out for You
The Cyber Security Tests, Certifications, and Solutions can assist device manufacturers, chip suppliers, and users to find the root of their problems or to fix and update the risks in the test reports, helping all parties to decrease the security risks in Bluetooth devices.
If you want to know more, we welcome you to visit Allion’s Cybersecurity Lab or contact us through this online form. Allion’s service team will gladly help you!
Technical Highlights